All Activity
- Yesterday
-
Кирил Осадчий joined the community
-
Release 4.3.8 LTS (preview, stable)*: Core: fixed a memory leak in the API parsers for IPv6 addresses and prefixes [NDM-4376] HTTP: addressed the CVE-2026-28753 security vulnerability in the web interface service [NDM-4368] HTTP: disabled HTTP/2 support to mitigate security vulnerabilities, including CVE-2026-49975, related to an HPACK out-of-memory (OOM) attack [NDM-4499] MWS: fixed the 'the controller DPN document is not accepted' error that occurred when acquiring an extender under certain conditions [NDM-4452] OpenSSL: library upgraded to 3.5.6/3.0.20 to address multiple security vulnerabilities [NDM-4402] CVE-2026-28386 CVE-2026-28387 CVE-2026-28388 CVE-2026-28389 CVE-2026-28390 CVE-2026-31789 CVE-2026-31790 SSH: fixed an issue that could prevent the session timeout from being applied correctly [NDM-4406] Wi-Fi: fixed a potential crash and memory leak that could occur when connecting to a Wi-Fi 7 network using WPA3-SAE after changing the wireless settings [SYS-1749] Wi-Fi: fixed the 2.4 GHz channel width display on models using MT7628 or MT7603 [SYS-1755] WireGuard: fixed the issue with multiple connections operation after a device restart (reported by @tkost, @Robespierre) [NDM-4418] * publication scope: KN-1111, KN-1211, KN-1212, KN-1311, KN-1511, KN-1611, KN-1711, KN-2210, KN-3010
- Last week
-
Vitalii Homon joined the community
-
Uladzimir Apenka joined the community
-
keen_parish27 started following Changelog 5.0 , Changelog 4.3 and Changelog 5.1
-
YghgStype joined the community
-
rulevoi joined the community
-
Release 5.0.12 (stable): Ethernet: resolved an issue in the Ethernet switch that affected the handling of 802.1Q frames with VLAN ID 0 [SYS-1785] HTTP: disabled HTTP/2 support to mitigate security vulnerabilities, including CVE-2026-49975, related to an HPACK out-of-memory (OOM) attack [NDM-4499] IP: improved the handling of non-exclusive FQDN-based routes when the destination interface is unavailable [NDM-4358] IPv6: fixed the 'ip policy no ipv6 route' command operation [NDM-4467] Mobile: added support for the six-digit PLMN mobile network operator identifier format in the command-line interface [SYS-1773] MWS: fixed the 'the controller DPN document is not accepted' error that occurred when acquiring an extender under certain conditions [NDM-4452] Web: resolved an issue that caused the wrong number of copies to be printed when users printed wireless network information from the mobile view (reported by @dimon27254) [NWI-4858]
-
maxgoglemogle joined the community
-
-Translate: mws zone [MAC] [CID] When the command is used, all Wi-Fi clients on the mesh network disconnect and reconnect after a few seconds. Could you design it so that this command can run live without any on/off switching?
-
Serg smelsg joined the community
-
KswgStype joined the community
-
It’s normal because the backhaul connection is still functioning - https://support.keenetic.com/titan/kn-1812/en/15237-what-hidden-wi-fi-networks-does-the-router-broadcast-.html
- 1 reply
-
- 1
-

-
Hi everyone, I have a Keenetic Titan KN 1812 and I've configured a schedule to automatically turn off the Wi-Fi during the night. The schedule works perfectly and the Wi-Fi actually turns off as expected. However, I noticed that the Wi-Fi LED on the router stays illuminated even when the wireless networks are disabled. Is this the normal/intended behavior for this model, or should the LED turn off together with the Wi-Fi? For reference, I am running the 5.0.11 version of KeeneticOS. Thanks in advance for your help!
- Earlier
-
Hi! Setup:Keenetic Titan (KN-1811), KeeneticOS 5.0.11, segments Main and IoT. I have the same issue. Tried : Relay multicast DNS enabled on both segments, firewall rules allowing UDP 5353 from IoT to any. Verified with `avahi-browse -at` from a Linux machine on Main — smart plugs (Shelly) devices on IoT never appear. Did anyone find a working solution purely within Keenetic's config?
-
Titan 1812 firmware version 5.0.11. Periodically, the router reboots a couple of times a day. There are Imou cameras on the network. Could that be the reason?
-
Release 5.1 Beta 4 (preview) MWS: fixed the 'the controller DPN document is not accepted' error that occurred when acquiring an extender under certain conditions [NDM-4452] Web: sorted the client list alphabetically when adding a custom view to the Traffic Monitor page (requested by @dimon27254) [NWI-4827] WireGuard: fixed the 'invalid I1 value' error that occured when importing certain configurations [NDM-4472]
-
In current KeeneticOS version 5.0.11, every time a "Read only" user logs in, a notification shows up in the lower right corner saying "The current user doesn't have permission to change device settings.". This (unnecessary) notification is exactly in the position where it hides the logout button, so the notification has to be dismissed just to be able to log out. Please either allow the notification to be dismissed permanently, or at least move it to a place where logging out is possible without dismissing it.
-
- 1
-

-
Hello, Adding another data point to the known PTK handshake issues on NC-1812. Environment: - Device: NC-1812 (Netcraze Ultra), chipset MT7992-BE7200 - Firmware: KeeneticOS 5.0.11 (stable, main channel) - Service tag: [fill in 15-digit code from device label] - Client: MacBook Pro M4 Max, macOS Tahoe 26.5 Symptom: The Mac cannot reliably connect to the 5GHz SSID (WifiMaster1). SAE key exchange completes, association succeeds, but the 4-way handshake fails at message 1 of 4. AP deauthenticates the client after a 5-second timeout. Router log (characteristic sequence): [I] WifiMaster1/AccessPoint0: STA(xx:xx:xx:xx:xx:xx) SAE key exchange done, PWE method: H2E. [I] WifiMaster1/AccessPoint0: STA(xx:xx:xx:xx:xx:xx) had associated (has FT caps). [I] WifiMaster1/AccessPoint0: STA(xx:xx:xx:xx:xx:xx) pairwise key handshaking timeout (msg 1 of 4-way). [I] WifiMaster1/AccessPoint0: STA(xx:xx:xx:xx:xx:xx) had deauthenticated by AP (reason: PTK 4-way handshake timeout). Key observations: 1. The issue occurs ONLY on the 5GHz radio (WifiMaster1). On 2.4GHz (WifiMaster0) the same client completes the handshake correctly ("set key done in WPA3/WPA3PSK"). 2. Other clients on the 5GHz radio connect normally — the bug is specific to the combination of MT7992 + macOS Tahoe. 3. The same Mac worked stably on this 5GHz network for several months before the macOS Tahoe upgrade. Tested on the router side (no effect): - Disabled Fast Transition (802.11r) - Disabled RRM/BTM (802.11k/v) - Disabled MLO, DL/UL MU-MIMO, DL/UL OFDMA, TWT, Airtime Fairness - Changed standard from 802.11a/n/ac/ax/be to 802.11a/n/ac/ax (without BE) - Changed channel width (160 → 80 → 40 MHz) - Tried different channels (UNII-1 / UNII-3) - Network protection: WPA2-PSK + WPA3-PSK transition, WPA2-only, WPA3-only - Full SSID removal and recreation Tested on the Mac side: - Removed network cache and re-added the network - Disabled Private Wi-Fi Address for this network - Disabled Bluetooth - Disabled iCloud Keychain sync for Wi-Fi The same Mac also has issues on another AP (Huawei AX3, HiSilicon Gigahome chipset) — confirming this is primarily a macOS Tahoe regression, not chipset-specific. However, MT7992 behaves more strictly: the connection cannot be established at all, while Huawei AX3 reconnects with packet loss. If a firmware-side mitigation is possible (e.g., increasing the PTK handshake timeout or making msg 1 retries more lenient), it could help users until Apple ships a fix. Thanks.
-
Hi everyone, I recently got a Titan 2 and I'd like to configure it to receive an IPv6 address from the Vodafone Italia fiber network. Given that the IPv4 connection works fine, I can't find (either through the web interface or CLI) the 'place' where I need to enter the 'host-uniq' parameter in hexadecimal (HEX), which is required to obtain an IPv6 address from the Vodafone Italia network. Has anyone managed to do this? Do you have a working configuration? Thanks!"
-
Please add a feature to change device region (consent and region settings). (http://192.168.1.100/rci/show/) I would like to switch from EAEU to EU and use EU cloud services. I prefer EU backend due to privacy and compliance considerations. Is there any official way to change this setting on a device level? For example, via UART access or Keenetic SDK?
-
Router Error. Webinterface without information
Memo posted a question in Dev channel issues & test reports
Hi, I have a KN-2410 and I keep having problems where I can't see any Wi-Fi settings or clients in the web interface. I have to restart it every time for it to work again. I've attached the logs. I'm using version 5.1 Beta 3, but this error also occurs with other versions. I also have the problem that when my mesh nodes are assigned static IPs, they no longer communicate properly with each other. log.txt -
Release 5.1 Beta 3 (preview) Ethernet: resolved an issue in the Ethernet switch that affected the handling of 802.1Q frames with VLAN ID 0 [SYS-1785] Mobile: added support for the newer 6-digit mobile network operator PLMN identifiers [NWI-4838] Web: resolved an issue with the Firewall Rule editor (reported by @spatiumstas) [NWI-4835] Web: resolved the issue with WISP connections to networks that have special characters in their names [NWI-4836]
-
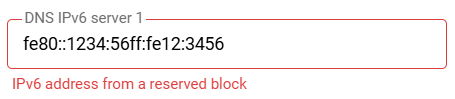
I solved my IPv6 and DNS problem. The problem: I didn't have IPv6 before, I used Adguard Home on a mini-PC for IPv4, and everything worked. After setting up to receive (dynamic) IPv6 from the provider, I found that the devices that run on IPv6 stopped accessing AdGuard Home. These devices accessed the router's DNS, and the router used some kind of global DNS (possibly the provider's DNS) instead of my Adguard Home. Solution: The devices generate Link-Local (fe80::) addresses for themselves. But the UI does not allow you to specify such an address as an IPv6 DNS address (I suppose there are reasons for this). But the UI allows you to specify a ULA (Unique Local Address (fd**::)) IPv6. Currently, by default, Keenetic does not enable the distribution of ULA addresses to devices. To enable this, run the command (on the <router address>/a or <router address>/ControlPanel/cli page) : OR to assign a random ULA IPv6 prefix: ipv6 local-prefix default OR to assign a specific ULA IPv6 prefix: ipv6 local-prefix fd00:caba::/48 (I found the commands here) Don't forget to save the changes: system configuration save Find the IPv6 address on the device (mini-pc/Raspberry), (for example, using ifconfig) and enter this IP in: My Networks and Wi-Fi → Home segment → DNS IPv6 server 1 After that, devices on the local network will receive IPv6 DNS belonging to the device with AdGuard Home and send DNS requests directly to it.
-
18/05/2026 Telegram Notifications Restored The technical issue has been resolved. Telegram notifications about sites and nodes changing to Online, Warning, and Offline statuses have been re-enabled and are now operating normally. Thank you for your understanding.
-
Access from Internet su GUI using Public IP Address
bobuzi replied to bobuzi's question in Feature Requests
RMM is always in beta, it's slow, RMM is not available as a self-hosted instance on my private cloud. Access to the GUI is done through the Keenetic proxy service external of my infrastrucure. This type of usage is not desired. I will explore others solutions for access GUI. -
Access from Internet su GUI using Public IP Address
Eug Family replied to bobuzi's question in Feature Requests
I use RMM for that. You can connect all the routers via VPN and access them all at once from one location. -
Access from Internet su GUI using Public IP Address
bobuzi replied to bobuzi's question in Feature Requests
"The connection is through keendns, through the priority provider, and in case of its disconnection, it automatically goes through the backup one." Ok, now it's more clear, but on my scenario, I need to access via GUI to all WAN and manage the device. This is all. -
Access from Internet su GUI using Public IP Address
Eug Family replied to bobuzi's question in Feature Requests
Do you use all 3 internets at the same time in load balancing mode or as a backup? I have 2 providers, it works in the main and secondary connect (back-up mode), with a public IP. The connection is through keendns, through the priority provider, and in case of its disconnection, it automatically goes through the backup one. -
Access from Internet su GUI using Public IP Address
bobuzi replied to bobuzi's question in Feature Requests
I agree with you that this type of access via IP and HTTP can be insecure. However, in complex deployments (for example, 3 WAN connections with 3 static public IPs), we need the ability to access the device through any of those connections. Using Keenetic KeenDNS works well in environments with a limited number of installed routers. But how does KeenDNS handle a scenario with 3 WANs and 3 public IPs? FQDN associated to on of 3 IPs... The requirement is to have selective access and full control of the device depending on the active WAN or reachable public IP. In addition, for each router it is necessary to generate a dedicated KeenDNS FQDN and maintain a complete inventory. Now imagine managing 100 routers, each with 2 or 3 public IP addresses. My interest is to access the GUI directly via IP address, preferably using HTTPS. Now via HTTP and IP work fine. -

Access from Internet su GUI using Public IP Address
corniger replied to bobuzi's question in Feature Requests
And if you want not the setting as it is currently implemented (ie to use direct mode KeenDNS name, which at moment works on a system primary connection, be noted - backup connections won't get pointed to until become primary), but actually post a feature request (as per forum section), then there's little chance it is automated. System would have to store certificate issued for IP address (not domain name), which is uncommon and also not secure. sorry I'm not telling more, as simple AI question reveals a bunch of 'why's it is not recommended even from a user point of view. In a case this address is dynamic, for one, router will have to request new certificate and revoke the old one each time the change happens, This is definitely not what your CA provider expects. And if you suddenly get the CG-NAT you instantly lose access (which wouldn't be a problem with KeenDNS solution, as it can automatically fall back to cloud base). I simply had a thought as there was an example above, where protocol is https and address is actually the IPv4 number. this is not how it works, usually Please confirm if you want specifically access via HTTPS protocol using cleartext IP of your router, and if that is the case, then any details you can share may be of help. -

Access from Internet su GUI using Public IP Address
corniger replied to bobuzi's question in Feature Requests
If you want to access over your public IPs, though, there's no need to set up anything apart from opening the HTTP access on the Management - Users & Access - Inbound Management Access: apply HTTP + HTTPS. mind that this will not be secure, as you'll be using plain http to open website by its IP address. not recommended in WAN scenario. recommended practice is to use KeenDNS - it has Direct mode where your traffic goes via your IP directly, not using cloud bounce all this is in KB by the way, try support section on the Keenetic website -
Release 5.1 Beta 2 (preview) Mobile: enabled the display of signal level, band, downlink and uplink frequency, BSSID, TAC/LAC, and PCI/PSC data, where available during mobile network scans with Hero 5G (KN-4110) devices [NWI-4800] MWS: added support for mobile network scanning with embedded 5G/4G modems on Wi-Fi System Extenders [NWI-4802] MWS: enabled the display of connection details for client devices connected to Wi-Fi System Extenders via Ethernet [NDM-4429] Web: adjusted the height of the list on the Application Traffic Analyser page (reported by @dimon27254) [NWI-4819] Web: resolved the issue that occurred when changing the network port speed on the System Settings page [NWI-4833] Web: updated the Wi-Fi Network Settings editor window to resolve the issue when configuring the WPA Enterprise protection [NWI-4806] Web: fixed the display of the current time in the schedule editor [NWI-4815] Web: resolved the scrolling issue for the mobile view of the Application Traffic Analyser page [NWI-4816] Web: fixed the display of transmitted traffic statistics for unregistered clients on the Client Lists page (reported by @x13) [NWI-4834] Web: fixed the Download Station application operation [NWI-4826] Web: fixed several issues with the Wi-Fi settings (reported by @spatiumstas, @keenet07) [NWI-4813] Web: adjusted the contrast of table elements to improve readability (requested by @spatiumstas) [NWI-4805] Web: removed the unnecessary 'Delete' button from the WireGuard VPN Server connection statistics window in mobile view [NWI-4809] Web: updated the Traffic Monitor card on the Dashboard page for better performance in mobile view [NWI-4779] Wi-Fi: updated the MediaTek Wi-Fi 7 SoC firmware and wireless driver to improve stability, compatibility, and performance in various Wi-Fi operation scenarios [SYS-1772] WireGuard: fixed the issue with multiple connections operation after a device restart (reported by @tkost, @Robespierre) [NDM-4418]
-
Device: Keenetic Ultra (NC-1812), hw_version 1218C000 Firmware: KeeneticOS 5.01.B.1.0-0 (5.1 Beta 1, preview channel, built Apr 18 2026) Chipset: MT7992-BE7200 (WiFi 7), SKU: #5.MT7992-BE7200-7975-7977 Resolved by: Downgrade to KeeneticOS 5.0 stable (main channel) Problem WiFi became completely unstable — both 2.4 GHz and 5 GHz bands affected simultaneously. Wired Ethernet worked perfectly throughout. The problem persisted across router reboots and WiFi radio restarts (interface WifiMaster0/1 down/up). Symptoms Wireless clients unable to auto-connect — must toggle WiFi off/on on the client device When connected, connection drops after seconds to minutes Drops are distance-dependent (worse at range) but also occur within 1 meter of the router After drop, clients get stuck in "zombie state" — they think they're connected but the router has already deauthenticated them Affects all client types: iPhones (iOS 18), iPads, Android (Galaxy S20 FE, Redmi A7 Pro), Huawei tablet, Denon AVR, Yandex Station, IoT sensors ~15 WiFi clients on the network Log evidence (from self-test and syslog) PTK 4-way handshake timeouts (router sends msg 1, client never responds): May 8 11:26:31 WifiMaster1/AccessPoint0: STA(ba:c3:32:22:e6:9e) pairwise key handshaking timeout (msg 1 of 4-way) May 10 19:36:31 WifiMaster0/AccessPoint0: STA(c4:82:e1:21:34:af) pairwise key handshaking timeout (msg 1 of 4-way) MIC corruption during key exchange: May 8 11:29:14 WifiMaster0/AccessPoint0: STA(1e:9f:6c:f6:d2:31) MIC differs in key handshaking May 8 12:45:19 — same device, repeated May 8 13:27:35 — same device, repeated Group key handshake timeout: May 9 12:00:14 WifiMaster1/AccessPoint0: STA(1e:9f:6c:f6:d2:31) group key handshaking timeout RSN IE failure: May 10 19:36:21 WifiMaster1/AccessPoint0: STA(1e:9f:6c:f6:d2:31) RSN IE sanity check failure (status code: 43) Mass simultaneous disconnection — all clients on both bands at once: May 10 19:42:57 WifiMaster0/AccessPoint0: STA(c4:82:e1:21:34:af) disassociated by AP (reason: due to inactivity) May 10 19:42:57 WifiMaster0/AccessPoint0: STA(00:06:78:4d:b7:9e) disassociated by AP (reason: due to inactivity) May 10 19:42:57 WifiMaster0/AccessPoint0: STA(82:a3:78:3d:23:24) disassociated by AP (reason: due to inactivity) May 10 19:42:57 WifiMaster0/AccessPoint0: STA(d4:12:43:ae:ef:62) disassociated by AP (reason: due to inactivity) May 10 19:42:57 WifiMaster1/AccessPoint0: STA(b2:92:d9:13:a9:53) disassociated by AP (reason: due to inactivity) May 10 19:42:57 WifiMaster1/AccessPoint0: STA(8c:c8:4b:a5:5f:db) disassociated by AP (reason: due to inactivity) May 10 19:42:57 WifiMaster1/AccessPoint0: STA(92:7a:20:d3:34:b1) disassociated by AP (reason: due to inactivity) May 10 19:42:57 WifiMaster1/AccessPoint0: STA(82:fe:44:93:b9:91) disassociated by AP (reason: due to inactivity) Constant "retransmits limit reached" for multiple devices across all 3 days. What was ruled out RF interference: Channel scan shows <10% load on both bands, minimal neighbor networks Neighbor issues: Adjacent apartments report no WiFi problems Channel selection: Tested manual channels (ch 11 on 2.4 GHz, ch 36/80 MHz on 5 GHz) — no improvement Band steering: Disabled via CLI — no improvement WPA3/FT: Disabled both — no improvement Radio restart: interface WifiMaster0/1 down/up — no improvement Router reboot: Full power cycle — no improvement Hardware failure: No kernel panics, watchdog resets, thermal warnings, or PHY errors in logs Configuration at time of issue SSID: same on both bands (band-steering enabled) Security: WPA2 + WPA3 (SAE), PMF, Fast Transition (802.11r) 2.4 GHz: auto channel, 20/40 MHz, BGN+AX+BE 5 GHz: auto channel, up to 160 MHz, AN+AC+AX+BE WireGuard VPN active USB storage (Seagate 2TB NTFS) attached Resolution Switching from preview channel (5.1 Beta 1) to main channel (5.0 stable) immediately resolved all WiFi issues. No configuration changes were needed — same settings work perfectly on 5.0. Self-test diagnostic files from during the issue are available on request.